Hacking
4 mins ago
Make An Linux Kernel Rootkit Visible Again
A make an LKM rootkit visible again. It involves getting the memory address of a…
CYBER SECURITY
2 hours ago
Do boards understand their new role in cybersecurity?
CIOs can start by arming their boards with the right questions, none of which are…
PYTHON
2 hours ago
imapautofiler 1.14.0 – sort-by-year action
What’s new in 1.14.0? add python 3.12 to test matrix add sort-by-year action
Computer Science
3 hours ago
A Guide to Access Controls – Communications of the ACM
With the increasing sophistication of cyber threats, implementing robust access controls is essential to ensure…
JAVA
4 hours ago
jOOQ 3.19 has been released with support for DuckDB, Trino, and much more
New Dialects It’s been a few releases since we’ve added support for new dialects, but…
Artificial Intelligence
4 hours ago
Empowering YouTube creators with generative AI
Technologies Published 18 September 2024 Authors Eli Collins New video generation technology in YouTube Shorts…
Data Science and ML
4 hours ago
Revolutionize logo design creation with Amazon Bedrock: Embracing generative art, dynamic logos, and AI collaboration
In the field of technology and creative design, logo design and creation has adapted and…
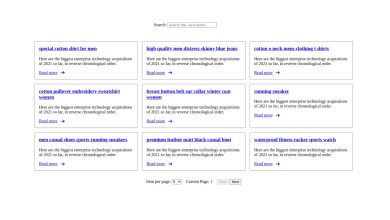
PROGRAMMING LANGUAGES
5 hours ago
Angular Search and pagination with example – Tech Incent
In this article, I will implement pagination and search for large amounts of data. This…
software engineering
5 hours ago
Proactive Measures Against Password Breaches and Cookie Hijacking
At Slack, we’re committed to security that goes beyond the ordinary. We continuously strive to…
Cloud Computing
5 hours ago
Boost Your Business And Empower Young Talent
Imagine walking into your office and seeing a vibrant team of young professionals buzzing with…