-
Hacking
Telegram for Android hit by a zero-day exploit – Week in security with Tony Anscombe
Video Attackers abusing the EvilVideo vulnerability could share malicious Android payloads via Telegram channels, groups, and chats, all while making…
Read More » -
Cloud Computing
Key Services & Commands Guide
The rise of cloud computing provides businesses the ability to quickly provision computing resources without the costly and laborious task…
Read More » -
CYBER SECURITY

Kicking dependency: Why cybersecurity needs a better model for handling OSS vulnerabilities
Modern software composition analysis needs reachability analysis The Endor Labs report emphasizes the role of modern software composition analysis (SCA)…
Read More » -
Data Science and ML

At 2024 AI Hardware & Edge AI Summit: Gayathri Radhakrishnan, Partner – Investment Team, Hitachi Ventures
At the recent 2024 AI Hardware & Edge AI Summit in San Jose, Calif., I caught up with Gayathri Radhakrishnan, Partner –…
Read More » -
Information Technology

You’ll be able to play your Nintendo Switch games on its successor
You don’t have to take great pains to preserve your Switch to ensure that you can still play your favorite…
Read More » -
Artificial Intelligence

Building a Robust Machine Learning Pipeline: Best Practices and Common Pitfalls
Building a Robust Machine Learning Pipeline: Best Practices and Common PitfallsImage by Editor | Midjourney In real life, the machine…
Read More » -
PYTHON

Avoid Counting in Django Pagination
This article looks at how to avoid the object count query in Django pagination. If you are using Postgres and…
Read More » -
Hacking

Pentesting for NIST 800-53, FISMA, and FedRAMP
Overview of NIST 800-53, FISMA, and FedRAMP The National Institute of Standards and Technology (NIST) is a U.S. federal agency…
Read More » -
CYBER SECURITY
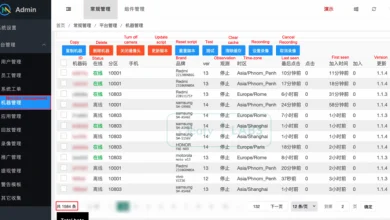
New Android Banking Malware ‘ToxicPanda’ Targets Users with Fraudulent Money Transfers
Nov 05, 2024Ravie LakshmananMobile Security / Cyber Attack Over 1,500 Android devices have been infected by a new strain of…
Read More » -
PROGRAMMING LANGUAGES
Fluid Everything Else | CSS-Tricks
We all know how to do responsive design, right? We use media queries. Well no, we use container queries now,…
Read More »
