ANY.RUN Discovers Tricky Phishing Attack Using Fake CAPTCHA – Latest Hacking News
Phishing campaigns relentlessly continue to evolve, utilizing innovative tricks to deceive users. ANY.RUN, the interactive malware analysis service, recently uncovered a phishing attack that takes advantage of fake CAPTCHA prompts to execute malicious scripts on victims’ systems.
In this phishing campaign, users are lured to a compromised website and are asked to complete a CAPTCHA, allegedly to verify their human identity or fix non-existent display errors on the page.
The moment they comply, the attackers exploit their trust by instructing them to run a malicious script via the Windows “Run” function (WIN+R). Specifically, users are tricked into executing a PowerShell script, which leads to system infection and potential compromise.
Stages of the attack
This phishing technique not only capitalizes on common web security practices like CAPTCHA verification but also adds a layer of urgency with fake error messages, increasing the likelihood of user compliance.
 Fake messages displayed to users
Fake messages displayed to users
ANY.RUN’s TI Lookup tool allows users to search for suspicious domains and investigate similar threats in detail.
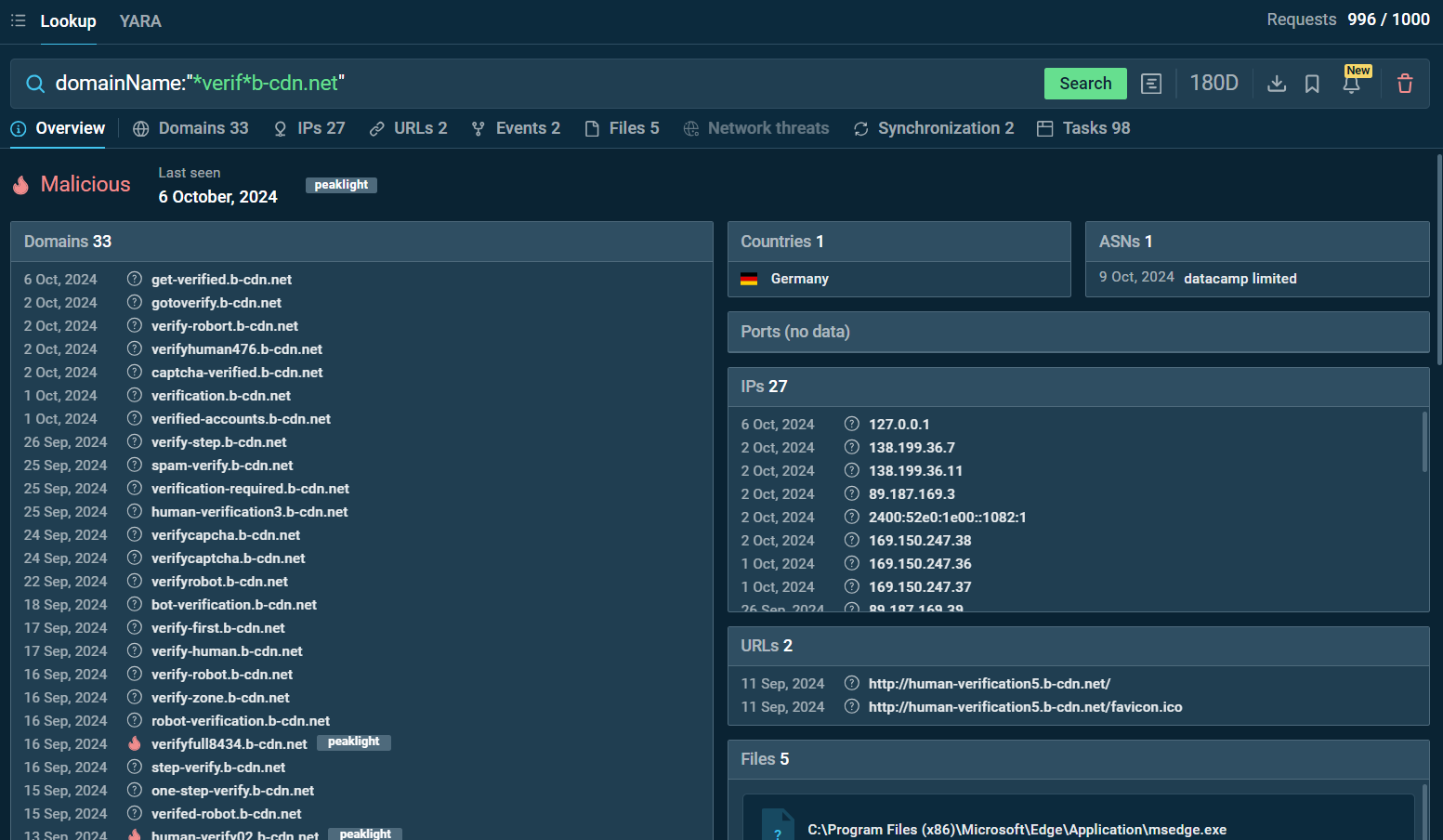 Search by the domain name “*verif*b-cdn.net” in ANY.RUN TI Lookup
Search by the domain name “*verif*b-cdn.net” in ANY.RUN TI Lookup
For instance, a search query for domainName:”*verif*b-cdn.net” or domainName:”*.human*b-cdn.net” in the TI Lookup tool reveals multiple associated domains, IP addresses and sandbox sessions linked to phishing activities.
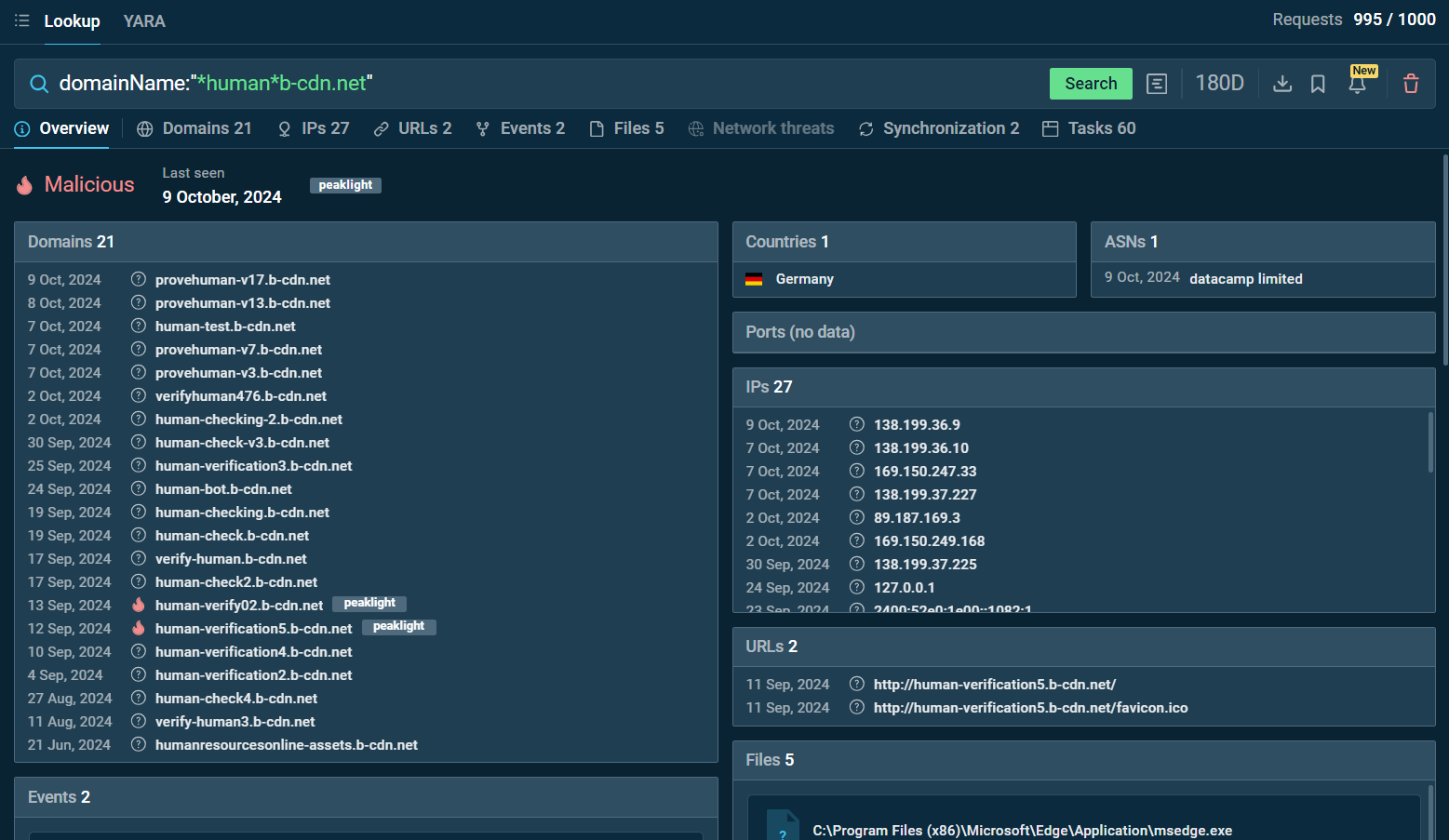 Search by the domain name “*.human*b-cdn.net” in ANY.RUN TI Lookup
Search by the domain name “*.human*b-cdn.net” in ANY.RUN TI Lookup
These queries provide critical insights into how these domains are leveraged to execute attacks, offering a clear view of the infrastructure behind the phishing campaign.
With ANY.RUN’s TI Lookup and sandbox working together, you can get a full picture of phishing campaigns and watch them unfold in real-time.
Sign up for a 14-day free trial to explore how ANY.RUN can assist your threat investigations.