Year: 2024
-
Data Science and ML
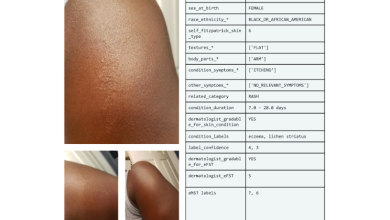
SCIN: A new resource for representative dermatology images
Posted by Pooja Rao, Research Scientist, Google Research Health datasets play a crucial role in research and medical education, but…
Read More » -
Cloud Computing

Shaping the Future of Cloud Sovereignty: Why you can’t afford to miss European Sovereign Cloud Day – In person (in Brussels) or Online (Virtual)
The global digital landscape is evolving at an unprecedented pace, and with it comes the mounting challenge of safeguarding data…
Read More » -
Latest IT Trends
Latest Trends
Provided to YouTube by Universal Music Group Latest Trends · A1 x J1 Latest Trends ℗ An EMI recording; ℗…
Read More » -
Artificial Intelligence
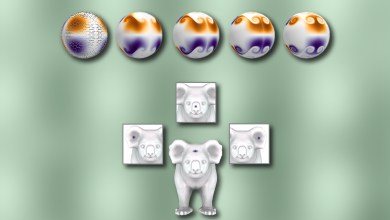
A framework for solving parabolic partial differential equations | MIT News
Computer graphics and geometry processing research provide the tools needed to simulate physical phenomena like fire and flames, aiding the…
Read More » -
software engineering

How Meta enforces purpose limitation via Privacy Aware Infrastructure at scale
At Meta, we’ve been diligently working to incorporate privacy into different systems of our software stack over the past few…
Read More » -
Information Technology

YouTube announces new AI tools for its creators: Veo, Communities, auto-dubbing, and more
At Made on YouTube on Wednesday, Sept. 18, in New York, YouTube CEO Neal Mohan announced various new AI tools…
Read More » -
Hacking
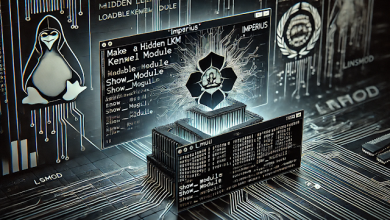
Make An Linux Kernel Rootkit Visible Again
A make an LKM rootkit visible again. It involves getting the memory address of a rootkit’s “show_module” function, for example,…
Read More » -
CYBER SECURITY

Do boards understand their new role in cybersecurity?
CIOs can start by arming their boards with the right questions, none of which are technical. For instance, have we…
Read More » -
PYTHON

imapautofiler 1.14.0 – sort-by-year action
What’s new in 1.14.0? add python 3.12 to test matrix add sort-by-year action
Read More » -
Computer Science

A Guide to Access Controls – Communications of the ACM
With the increasing sophistication of cyber threats, implementing robust access controls is essential to ensure only authorized personnel can access…
Read More »
