Year: 2024
-
CYBER SECURITY

Microsoft summit plots end of kernel access for EDR security clients
Microsoft has dropped heavy hints that change is coming to the way security products interact with the critical core of…
Read More » -
Artificial Intelligence

Study: Transparency is often lacking in datasets used to train large language models | MIT News
In order to train more powerful large language models, researchers use vast dataset collections that blend diverse data from thousands…
Read More » -
software engineering
Improving Efficiency Of Goku Time Series Database at Pinterest (Part — 3) | by Pinterest Engineering | Pinterest Engineering Blog | Sep, 2024
Monil Mukesh Sanghavi; Software Engineer, Real Time Analytics Team | Ming-May Hu; Software Engineer, Real Time Analytics Team | Xiao…
Read More » -
Computer Science

Kickstart Your Career with a Python Techdegree [Article]
Are you ready to kickstart your career in tech, but don’t want to cover the cost of a four-year degree?…
Read More » -
PROGRAMMING LANGUAGES

What’s faster, COUNT(*) or COUNT(*) with LIMIT in SQL? Let’s check
In a previous blog post, we’ve advertised the use of SQL EXISTS rather than COUNT(*) to check for existence of…
Read More » -
Computer Science

The Download: An AI safety hotline, and tech for farmers
—Kevin Frazier is an assistant professor at St. Thomas University College of Law and senior research fellow in the Constitutional…
Read More » -
software engineering

Startups: How to Avoid Bad Product Design
Young companies can’t afford to make mistakes: An estimated 90% of startups fail, according to the research and policy advisory…
Read More » -
CYBER SECURITY

Designing an Identity-Focused Incident Response Playbook
Sep 16, 2024The Hacker NewsIdentity Protection / Incident Response Imagine this… You arrive at work to a chaotic scene. Systems…
Read More » -
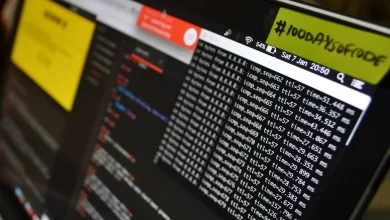
Hacking
ModTracer – ModTracer Finds Hidden Linux Kernel Rootkits And Then Make Visible Again
ModTracer Finds Hidden Linux Kernel Rootkits and then make visible again. Another way to make an LKM visible is using the imperius trick: https://github.com/MatheuZSecurity/Imperius…
Read More » -
Data Science and ML
Top 5 Benefits of Zero Trust Network Access for Small and Medium Businesses
With the increasing advancement in digital platforms and applications, small and medium-sized businesses (SMBs) are at high risk of cyber…
Read More »
